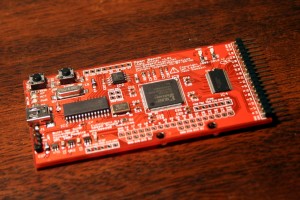
Way back in 2010, I came across the Open Bench Logic Sniffer (OLS) from Dangerous Prototypes. Being in the market for an inexpensive, capable logic sniffer that I can use with open-source GNU/Linux tools, and being a sucker for red circuit boards, I snapped one right up. Three years later, I finally got it working.
My initial experience with the device revealed three major problems:
- The software used to interface with the OLS and capture samples is crummy.
- The firmware is immature and glitchy.
- I have no idea how to use a logic sniffer.
Complicating matters is the fact that the online documentation is disorganized and confusing. I still can’t figure out the relationship between Dangerous Prototypes and Gadget Factory… So after sitting unused in my toolbox for three years, I decided to give it another go. Since I first bought the OLS, the original SUMP client has been supplanted by the unimaginatively-named Logic Sniffer client. While still a little buggy, it is easier to use and has more features than the SUMP client. So that pretty much takes care of problem (1). Problem (2) is what I primarily set out to address. The device I bought is hardware version 1.01. Current models are version 1.04. More importantly, the firmware running on the PIC and the FPGA bitstream have advanced considerably. I’m not sure which firmware/FPGA versions shipped with my device, but I know that the firmware was pre-1.0 and the FPGA was running the original SUMP core. As of this writing, the latest firmware is version 3.0 and the latest bitstream is Demon core 3.07. It took a lot of digging though webpages and forums, but I finally managed to get new code loaded. Here’s how.
- Get the latest code from Gadget Factory’s download page. For me, that’s Linux Expert 3.08 Inside, there’s a folder containing the analyzer software and a folder containing firmware and upgrade tools. I’m running Ubuntu 12.04 LTS 64-bit, so the upgrade tools I used are in the linbin64 folder. If you are on a 32-bit system, use the linbin folder. As far as I can tell, the tools work the same way, save for some obnoxious inconsistencies in the nomenclature (ols_fw_update vs. ols-fw-update). There is an included script (ols-upgrader.sh) that is supposed to automate everything, but it simply didn’t work for me.
- Plug in the OLS and determine which port it’s connected to. For me, it’s /dev/ttyAMC0.
$ dmesg|tail [88170.239027] usb 1-4.3: New USB device found, idVendor=04d8, idProduct=fc92 [88170.239032] usb 1-4.3: New USB device strings: Mfr=1, Product=2, SerialNumber=0 [88170.239036] usb 1-4.3: Product: Logic Sniffer CDC-232 [88170.239039] usb 1-4.3: Manufacturer: Microchip Technology Inc. [88170.239456] cdc_acm 1-4.3:1.0: This device cannot do calls on its own. It is not a modem. [88170.239476] cdc_acm 1-4.3:1.0: ttyACM0: USB ACM device
Notice that idVendor is 0x04D8 and idProduct is 0x0FC92. The Product ID was 0x000A in the old firmware, so you’ll see both IDs in documentation across the web. - First, we load the new FPGA bitsream. Put the OLS in ROM update mode by holding down the UPDATE button and pushing REST. The two green LEDs, ACT and PWR, should light. For peace of mind, I like to run the self test before proceeding. It tells you the code version on the device and gives you a smiley face if it checks out.
$ sudo ./ols-loader -selftest -p:/dev/ttyACM0 Logic Sniffer ROM loader v0.3 (November 9, 2010) Opening serial port '/dev/ttyACM0' @ 921600 ... OK Found OLS HW: 1, FW: 3.0, Boot: 1 Found flash: ATMEL AT45DB041D done... Passed self-test :)
Now that we feel warm and fuzzy, let’s load the FPGA bitsream into ROM.$ sudo ./ols-loader -write -erase -p:/dev/ttyACM0 -wB:FPGAROM/logic_sniffer_3.07-Demon-Core.bit Logic Sniffer ROM loader v0.3 (November 9, 2010) Opening serial port '/dev/ttyACM0' @ 921600 ... OK Found OLS HW: 1, FW: 3.0, Boot: 1 Found flash: ATMEL AT45DB041D Chip erase ... done :) Reading BIN file '../FPGAROM/logic_sniffer_3.07-Demon-Core.bit' ... OK! (binary size = 169314) Will write 642 pages Page 0x0000 write ... (0x0000 0x0000)OK ...
- To update the PIC firmware, we must first enter bootloader mode. This can be accomplished by placing a jumper between the PGC and PGD pins on the ICSP header during a reset, or with the ols-loader utility.
$ sudo ./ols-loader -p:/dev/ttyACM0 -boot Logic Sniffer ROM loader v0.3 (November 9, 2010) Opening serial port '/dev/ttyACM0' @ 921600 ... OK Found OLS HW: 1, FW: 3.0, Boot: 1 Found flash: ATMEL AT45DB041D OLS switched to bootloader mode
Verify that the OLS is actually in bootloader mode by checkingDMESGfor something like this:$ dmesg|tail [91046.142568] usb 1-4.3: Product: Diolan [91046.142572] usb 1-4.3: Manufacturer: Diolan [91046.143865] hid-generic 0003:04D8:FC90.0003: hidraw2: USB HID v1.01 Device [Diolan Diolan] on usb-0000:00:1a.7-4.3/input0
The same product and vendor IDs show up, but the OLS is now showing up as a human interface device (HID). This means that the USB bootloader, written by Diolan, is now running the show on the PIC. - Now is when we need to pay attention to the vendor ID. Make sure to set the -vid flag with whatever is appropriate for your device, so that the firmware update tool can find your OLS. Once you’re done updating the firmware, however, it should have a VID of 0x04D8.
$ sudo ./ols_fw_update -e -w -m flash -vid 0x04d8 -pid 0xfc90 -ix ../PIC_firmware/OLSv1.firmware.v3.0.hex U2IO flash erasing: DONE. U2IO flash programming: DONE. RESET Device Operation successfully completed.
Since I have a hardware v1.01 device, I used the OLSv1 firmware. However, there is firmware in the PIC_firmware directory labeled as v1.04. I don’t know what the difference is, so choose whatever you feel is appropriate. - Huzzah! You’ve updated your OLS to be better than ever. Bask in the glory of your victory by sniffing some UART.
This entry on microtherion’s blog is an excellent resource for anyone else trying to untangle the confusing mess of information on the OLS, and was a tremendous help for my own work.